smart cards tokens security and applications pdf This state-of-the art work combines a cross-discipline overview of smart cards, . AUBURN, Ala. (AP) — Rod Bramblett, the longtime radio announcer for Auburn football and basketball games, and his wife were killed in a two-vehicle accident. He was 53. .
0 · what is smart card number
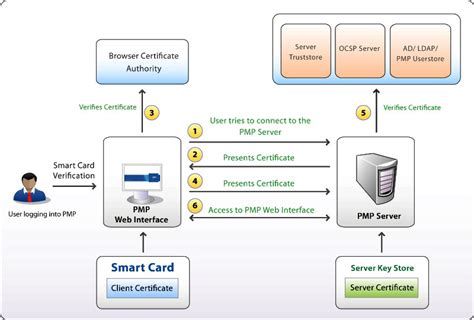
1 · what is smart card authentication
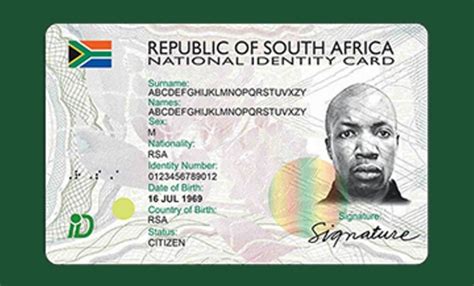
2 · smart card identity
3 · smart card identification
4 · smart card based identification system
5 · smart card based authentication
6 · memory based smart card
7 · azure smart card authentication
Auburn Tigers. Get live coverage of SEC college football games with home and away feeds for every team on SiriusXM, including the Auburn Tigers. Hear exclusive interviews with Auburn players and coaches, plus expert analysis .
A step-by-step approach educates the reader in card types, production, operating systems, .
presents the main features of smart card technology in the light of the EMV card specificati.
what is smart card number
what is smart card authentication
This state-of-the art work combines a cross-discipline overview of smart cards, .presents the main features of smart card technology in the light of the EMV card . A step-by-step approach educates the reader in card types, production, .A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.
This state-of-the art work combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.Chapter 9: “Smart Card Security” gives a very good introduction of the different types of attacks that may apply to smart cards. It briefly describes invasive attacks. The focus is on semi-invasive and non-invasive attacks. He presents the different categories of side channel attacks. The author clearly likes the
presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. This chapter provides a first introduction to a wide range of smart cards and tokens, considering the various types, capabilities, popular applications and the practicality of their. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development,.
This book combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.Smart Cards, Tokens, Security and Applications. This book provides a broad overview of the many card systems and solutions that are in practical use today. This new edition adds content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking or payment cards, identity cards and passports, mobile systems .A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.
This state-of-the art work combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development, deployment and lifecycle management.Chapter 9: “Smart Card Security” gives a very good introduction of the different types of attacks that may apply to smart cards. It briefly describes invasive attacks. The focus is on semi-invasive and non-invasive attacks. He presents the different categories of side channel attacks. The author clearly likes the
smart card identity
presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. This chapter provides a first introduction to a wide range of smart cards and tokens, considering the various types, capabilities, popular applications and the practicality of their. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new technologies, security design, attacks, application development,. This book combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.

smart card identification
smart card based identification system
smart card based authentication
memory based smart card
Fans can listen to free, live streaming audio of Auburn Sports Network radio .
smart cards tokens security and applications pdf|smart card based identification system