authentication smart card How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. $54.25
0 · smart card multi factor authentication
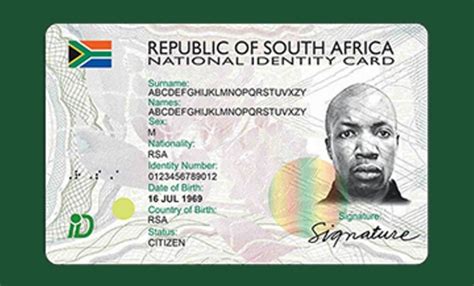
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
The problems seems to be that it's not possible to emulate/modify the sector 0, which is often the UID (identifier). This question is linked (but probably outdated). It is possible .
smart card multi factor authentication
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that .How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.

how to remove rfid chip from oyster card
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that . Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in .Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and .
Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is . Smart Card Authentication is how identity is checked using a smart card. The smart card has a microchip that can securely store and work with information. It contains data that .
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data .Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or .Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the .
Smart Card Authentication. Offering a range of certificate-based PKI smart cards with strong multi-factor authentication. Our Smart card authentication meets the highest security standards!How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system.Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that . Smart cards are tamper-resistant portable storage devices that can enhance the security of tasks such as authenticating clients, signing code, securing e-mail, and signing in .
Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and .Smart card authentication requires two things: the smart card itself and a pin entered by the user. With smart cards there are two different ways to authenticate yourself into a system, there is . Smart Card Authentication is how identity is checked using a smart card. The smart card has a microchip that can securely store and work with information. It contains data that . Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data .
Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or .Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the .
smart card identity
smart card based identification system
http hackaday.com 2011 05 20 using-an-avr-as-an-rfid-tag
smart card authentication step by
A Wave profile allow you to instantly exchange professional information with .
authentication smart card|smart card identity