ssh config smart card Server configuration. The SSH server and client must be configured to permit . What Is NFC Tag Reader iPhone? iOS apps running on supported devices can use NFC scanning to read data from electronic tags attached to real-world objects. In-App Tag Reading. An application can enable single- or .
0 · Smart card authentication with SSH
1 · Smart card authentication
2 · Smart Card Logon for SSH
3 · Smart
4 · Managing smart card authentication
5 · Chapter 6. Configuring smart card authentication with local
6 · About SSH and Smart Card support (RHEL 7)
The ACR1255U-J1 ACS Secure Bluetooth® NFC Reader supports ISO 14443 Type A and B smart cards, MIFARE®, FeliCa, and most NFC tags and devices compliant with ISO 18092 standard. The ACR1255U-J1 has both .
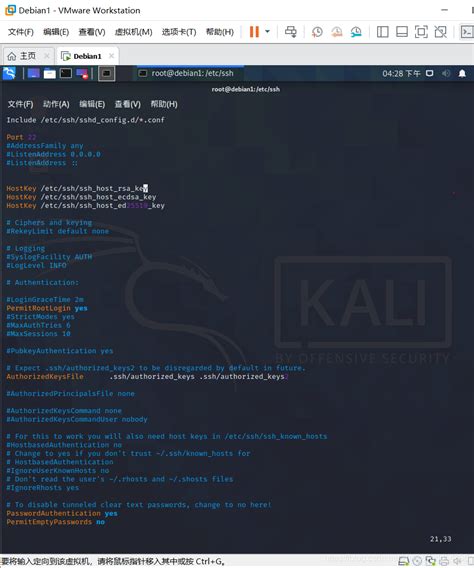
The SSH server and client must be configured to permit smart card authentication. Configure the SSH server. The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key. Ensure the server has the PubkeyAuthentication option set .Server configuration¶ The SSH server and client must be configured to permit .Server configuration. The SSH server and client must be configured to permit .
Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this . Server configuration¶ The SSH server and client must be configured to permit smart card authentication. Configure the SSH server¶ The SSH server needs to allow public key .You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect.You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect. Use the following configuration to accomplish this scenario: Obtain .
Server configuration. The SSH server and client must be configured to permit smart card authentication. Configure the SSH server. The SSH server needs to allow public key .
Smart card authentication with SSH
Gnome in RHEL7 was relying on pam_pkcs11 to provide access to Smart Cards through NSS. In RHEL8+, the desktop login is managed by System Security Services Daemon (SSSD). How to .Abstract. With Red Hat Identity Management (IdM), you can store credentials in the form of a private key and a certificate on a smart card. You can then use this smart card instead of .PAM configuration. To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on .The SSH server and client must be configured to permit smart card authentication. Configure the SSH server. The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key. Ensure the server has the PubkeyAuthentication option set to ‘yes’ in its /etc/ssh/sshd_config file. In a .
Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this guide will help you configure a .
Smart card authentication
Server configuration¶ The SSH server and client must be configured to permit smart card authentication. Configure the SSH server¶ The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key.The connection to remote server can be issued using this command (a smart card is usually protected by PIN so you are prompted before accessing the operation on the card): [localhost ~] $ ssh -I /usr/lib64/pkcs11/opensc-pkcs11.so hostname Enter PIN for 'Test (UserPIN)': [hostname ~] $ Client configuration. Additionally, you can store the path .
You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect.
You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect. Use the following configuration to accomplish this scenario: Obtain a user certificate for the user who wants to authenticate with a smart card.Server configuration. The SSH server and client must be configured to permit smart card authentication. Configure the SSH server. The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key.
Gnome in RHEL7 was relying on pam_pkcs11 to provide access to Smart Cards through NSS. In RHEL8+, the desktop login is managed by System Security Services Daemon (SSSD). How to configure system to allow smart cards login of users in IdM is described in RHEL 8 Product documentation, section Configuring Identity Management.Abstract. With Red Hat Identity Management (IdM), you can store credentials in the form of a private key and a certificate on a smart card. You can then use this smart card instead of passwords to authenticate to services. Administrators can configure mapping rules to reduce the administrative overhead.PAM configuration. To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need.
azure adfs smart card
The SSH server and client must be configured to permit smart card authentication. Configure the SSH server. The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key. Ensure the server has the PubkeyAuthentication option set to ‘yes’ in its /etc/ssh/sshd_config file. In a .Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this guide will help you configure a .
Server configuration¶ The SSH server and client must be configured to permit smart card authentication. Configure the SSH server¶ The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key.The connection to remote server can be issued using this command (a smart card is usually protected by PIN so you are prompted before accessing the operation on the card): [localhost ~] $ ssh -I /usr/lib64/pkcs11/opensc-pkcs11.so hostname Enter PIN for 'Test (UserPIN)': [hostname ~] $ Client configuration. Additionally, you can store the path .You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect.
You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect. Use the following configuration to accomplish this scenario: Obtain a user certificate for the user who wants to authenticate with a smart card.Server configuration. The SSH server and client must be configured to permit smart card authentication. Configure the SSH server. The SSH server needs to allow public key authentication set in its configuration file and it needs the user’s public key.Gnome in RHEL7 was relying on pam_pkcs11 to provide access to Smart Cards through NSS. In RHEL8+, the desktop login is managed by System Security Services Daemon (SSSD). How to configure system to allow smart cards login of users in IdM is described in RHEL 8 Product documentation, section Configuring Identity Management.Abstract. With Red Hat Identity Management (IdM), you can store credentials in the form of a private key and a certificate on a smart card. You can then use this smart card instead of passwords to authenticate to services. Administrators can configure mapping rules to reduce the administrative overhead.
barclays smart card operation terminated

Smart Card Logon for SSH
Proceed as follows: First open the Settings app on your iPhone. Then select the option “Control .
ssh config smart card|About SSH and Smart Card support (RHEL 7)