explain like i five smart cards pki maintains data integrity Public key infrastructure is an important aspect of internet security. It is the set of technology and processes that make up a framework of encryption to protect and authenticate digital . See more The Halo II provides added peace-of-mind from enhanced security features at an affordable .
0 · why pki is important
1 · pki security basics
2 · pki data integrity
3 · pki basics explained
4 · how to use pki
5 · fundamentals of pki
6 · federal pki key infrastructure
7 · basics of pki 101
For personal use only. Airtime expires after 180 days of last use or 30 days after .

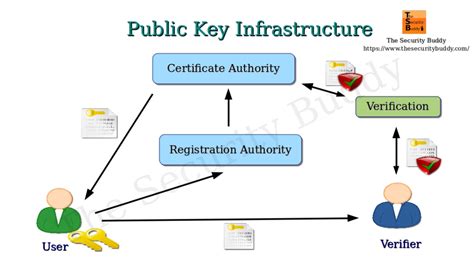
Public key infrastructure is an important aspect of internet security. It is the set of technology and processes that make up a framework of encryption to protect and authenticate digital . See moreOne of the most common uses of PKI is the TLS/SSL (transport layer security/secure socket layer), which secures encrypted HTTP (hypertext transfer protocol) . See morePublic key infrastructure uses asymmetric encryption methods to ensure that messages remain private and also to authenticate the . See more
The core of a public key infrastructure is trust. It is important for a recipient entity to know without a doubt that the sender of the digital certificate is exactly who they claim to be. Trusted . See moreOpen-source public key infrastructure is publicly available. Examples of open-source PKI include the following: 1. EJBCA Enterprise: . See moreFederal PKI credentials reduce the possibility of data breaches that can result from using weak credentials, such as username and password. Specifically, the Federal PKI closes security . Unlike encryption, which is a two-way function because encrypted data is intended to be reversed, hashing isn’t meant to be reverse engineered. It protects data integrity by .
Data Integrity: PKI guarantees data integrity by allowing recipients to verify that information has not been tampered with during transit. This is essential for critical operations like financial .
why pki is important
Data on a website can be protected using a secure socket layer (SSL) certificate, which establishes an encrypted link between a web browser and a server. It also protects the .Public Key Infrastructure (PKI) uses asymmetric cryptography to secure confidential information, authenticate users, & validate the integrity and origin of a message. 1. Confidentiality — Data Encryption: PKI employs encryption techniques to protect sensitive information from unauthorized access. Data encryption ensures that data remains . What is the need for Public Key Infrastructure? PKI is significant because it provides a safe and dependable way to certify the identity of communication parties and .
Public Key Infrastructure (PKI) is important because it significantly increases the security of a network and provides the foundation for securing all internet-connected things. PKI is a core .
pki security basics
PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates.Federal PKI credentials reduce the possibility of data breaches that can result from using weak credentials, such as username and password. Specifically, the Federal PKI closes security gaps in user identification and authentication, encryption of sensitive data, and data integrity.
Unlike encryption, which is a two-way function because encrypted data is intended to be reversed, hashing isn’t meant to be reverse engineered. It protects data integrity by informing you about whether data has been altered since it was signed. To learn more, check out our article on hashing vs encryption.
Data Integrity: PKI guarantees data integrity by allowing recipients to verify that information has not been tampered with during transit. This is essential for critical operations like financial transactions and healthcare records.Data on a website can be protected using a secure socket layer (SSL) certificate, which establishes an encrypted link between a web browser and a server. It also protects the integrity of data when in transit between a server or firewall and the web browser.
Public Key Infrastructure (PKI) uses asymmetric cryptography to secure confidential information, authenticate users, & validate the integrity and origin of a message. 1. Confidentiality — Data Encryption: PKI employs encryption techniques to protect sensitive information from unauthorized access. Data encryption ensures that data remains confidential during. What is the need for Public Key Infrastructure? PKI is significant because it provides a safe and dependable way to certify the identity of communication parties and ensure the confidentiality and integrity of data exchanged through networks. It achieves this using digital certificates and public and private key encryption.
best rfid jamming card
Public Key Infrastructure (PKI) is important because it significantly increases the security of a network and provides the foundation for securing all internet-connected things. PKI is a core component of data confidentiality, information integrity, authentication, and data access control.Public Key Infrastructure or PKI is a cost effective tool to ensure the confidentiality, integrity, and availability of electronic transactions. PKI utilizes asymmetric cryptography, meaning a different key is used to encrypt (public key) than is used to decrypt (private key).
PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates.Federal PKI credentials reduce the possibility of data breaches that can result from using weak credentials, such as username and password. Specifically, the Federal PKI closes security gaps in user identification and authentication, encryption of sensitive data, and data integrity. Unlike encryption, which is a two-way function because encrypted data is intended to be reversed, hashing isn’t meant to be reverse engineered. It protects data integrity by informing you about whether data has been altered since it was signed. To learn more, check out our article on hashing vs encryption.
Data Integrity: PKI guarantees data integrity by allowing recipients to verify that information has not been tampered with during transit. This is essential for critical operations like financial transactions and healthcare records.Data on a website can be protected using a secure socket layer (SSL) certificate, which establishes an encrypted link between a web browser and a server. It also protects the integrity of data when in transit between a server or firewall and the web browser.Public Key Infrastructure (PKI) uses asymmetric cryptography to secure confidential information, authenticate users, & validate the integrity and origin of a message. 1. Confidentiality — Data Encryption: PKI employs encryption techniques to protect sensitive information from unauthorized access. Data encryption ensures that data remains confidential during.
are rfid tags rewritable
What is the need for Public Key Infrastructure? PKI is significant because it provides a safe and dependable way to certify the identity of communication parties and ensure the confidentiality and integrity of data exchanged through networks. It achieves this using digital certificates and public and private key encryption.Public Key Infrastructure (PKI) is important because it significantly increases the security of a network and provides the foundation for securing all internet-connected things. PKI is a core component of data confidentiality, information integrity, authentication, and data access control.
pki data integrity
Los Angeles Rams quarterback Matthew Stafford (9) and Detroit Lions quarterback Jared Goff (16) during an NFC Wild Card round football game against the Los Angeles Rams on January 14, 2024 in Detroit. (Jeff Nguyen/Detroit .Detroit Lions 37 at Philadelphia Eagles 58 on December 30th, 1995 - Full team and player stats and box score . Wild Card - Detroit Lions at Philadelphia Eagles - December 30th, 1995. via .
explain like i five smart cards pki maintains data integrity|federal pki key infrastructure