linux ssh smart card Use this method to enforce SSH smart card login on a per user basis. After this step you can SSH into the server using the smart card for authentication. To transfer your money faster than one to two business days, you have several .Are you ready to bust three myths about contactless cards? So let's jump right in. Three myths about the dangers of contactless cards. See more
0 · Smart card authentication with SSH
1 · Smart card authentication
2 · Smart Card Logon for SSH
3 · Smart
4 · Managing smart card authentication
5 · How to Set up SmartCard Authentication on Linux
6 · How can I set up smart card SSH authentication?
7 · Chapter 6. Configuring smart card authentication with local
8 · About SSH and Smart Card support (RHEL 7)
Our Test SIMs help you to verify the compliance of mobile devices with the latest industry standards. This way they improve product quality and safety. In order to meet the growing challenges of quality and conformity, we .Yes, you can accept credit card payments for your business using your phone and a payment processing service. This payment acceptance method is referred to as “mobile POS” and typically includes a mobile payment processing app that connects with a credit card reader. The best mobile POS systemscan also . See more
Most of the cards are read-only and do not need this step. If your card is issued by the third party (a government), you already have pre-generated keys and . See moreConnecting using public key in SSH requires the presence of the public key on the server to verify clients signatures. If we don't have the public key stored . See moreOne of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner .Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS .
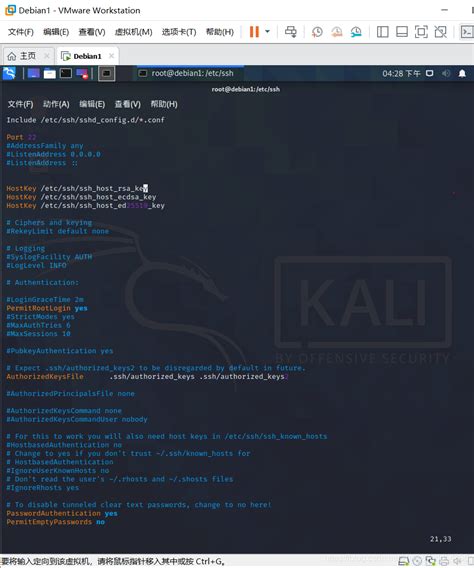
Use this method to enforce SSH smart card login on a per user basis. After this step you can SSH into the server using the smart card for authentication.
To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 .
One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner .In Red Hat Enterprise Linux, we strive to support several popular smart-card types. However, because it is not possible to support every smart card available, this document specifies our .
If you are using your smart card to authenticate using SSH, you need to add the full certificate to the user entry in Identity Management (IdM). If you are not using your smart card to .To configure smart card authentication with local certificates: The host is not connected to a domain. You want to authenticate with a smart card on this host. You want to configure SSH . It can be used to configure smart card authentication on a Linux system by using the "smartcard" auth provider. And configure PAM (Pluggable Authentication Modules) to use .
This article describes the supported way of setting up and using smart cards for authentication in Secure Shell for Red Hat Enterprise Linux 7.One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this guide will help you configure a . Use this method to enforce SSH smart card login on a per user basis. After this step you can SSH into the server using the smart card for authentication.
To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need.One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.
In Red Hat Enterprise Linux, we strive to support several popular smart-card types. However, because it is not possible to support every smart card available, this document specifies our targeted cards.
If you are using your smart card to authenticate using SSH, you need to add the full certificate to the user entry in Identity Management (IdM). If you are not using your smart card to authenticate using SSH, you can add certificate mapping data using the ipa user-add-certmapdata command.
To configure smart card authentication with local certificates: The host is not connected to a domain. You want to authenticate with a smart card on this host. You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect. It can be used to configure smart card authentication on a Linux system by using the "smartcard" auth provider. And configure PAM (Pluggable Authentication Modules) to use SSSD for smart card authentication.
rfid chip hoax
This article describes the supported way of setting up and using smart cards for authentication in Secure Shell for Red Hat Enterprise Linux 7.One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.
Smart Card Logon for SSH For network engineers, this guide will help you authenticate with your PIV/CAC credential and use SSH to access a remote Linux server from a Windows or macOS computer. For server administrators, this guide will help you configure a . Use this method to enforce SSH smart card login on a per user basis. After this step you can SSH into the server using the smart card for authentication.To enable smart card authentication we should rely on a module that allows PAM supported systems to use X.509 certificates to authenticate logins. The module relies on a PKCS#11 library, such as opensc-pkcs11 to access the smart card for the credentials it will need.One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.
In Red Hat Enterprise Linux, we strive to support several popular smart-card types. However, because it is not possible to support every smart card available, this document specifies our targeted cards.If you are using your smart card to authenticate using SSH, you need to add the full certificate to the user entry in Identity Management (IdM). If you are not using your smart card to authenticate using SSH, you can add certificate mapping data using the ipa user-add-certmapdata command.To configure smart card authentication with local certificates: The host is not connected to a domain. You want to authenticate with a smart card on this host. You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect.
Smart card authentication with SSH
rfid chip in football
rfid chip implant new born children between 2015 2019
rfid chip in eye laser
rfid chip implant sydney
If you often work with NFC tags, NFC Reader Writer will make this process more efficient. With its simple interface and clear menu, the app is great for novice users. Learn all the features of NFC quickly and for free.
linux ssh smart card|Managing smart card authentication